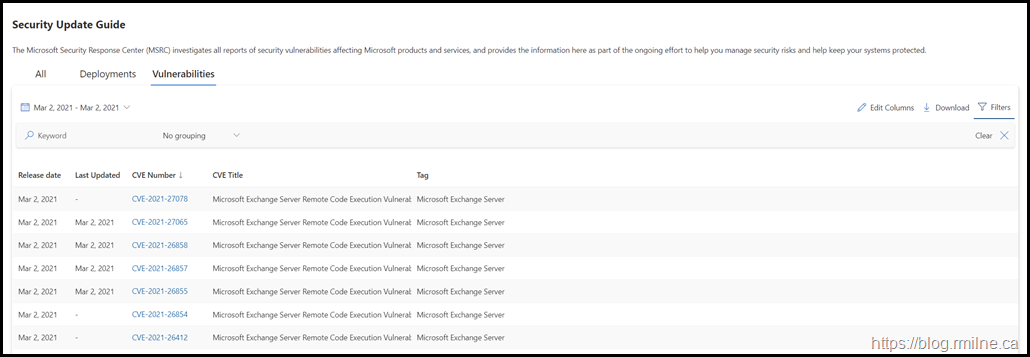
Security updates were released today for Exchange 2010, 2013, 2016 and 2019. Attacks were detected which leveraged these vulnerabilities, so an out of band set of updates was released
This a remote code execution on TCP 443 and is already being exploited as a 0-Day attacks against on-premises Exchange servers.
Microsoft strongly recommends installing this update immediately. Internet facing servers should be prioritised, followed by the remaining Exchange servers.
One patching has completed, read the articles below to perform advanced hunting.
A separate post with collated links is: Collected Links For Hafnium – March 2021 Exchange Security Issue
Recommended Reading
HAFNIUM targeting Exchange Servers with 0-day exploits - Microsoft Security
Released: March 2021 Exchange Server Security Update
Updates are available for:
-
Exchange Server 2010 (RU 31 for Service Pack 3 – this is a Defense in Depth update)
-
Exchange Server 2013 (CU 23)
-
Exchange Server 2016 (CU 19, CU 18)
-
Exchange Server 2019 (CU 8, CU 7)
Manual Update Download
You can download the update for Exchange 2013, 2016 and 2019 here:
Description of the security update for Microsoft Exchange Server 2019, 2016, and 2013: March 2, 2021 (KB5000871)
Manual Update Download – Exchange 2010
For those still running Exchange 2010, the update can be downloaded here:
Description of the security update for Microsoft Exchange Server 2010 Service Pack 3: March 2, 2021 (KB5000978)
Bootnote
You must be on a version of Exchange which supports the installation of the update. For example, if you are still on Exchange 2013 CU22, then you must upgrade to CU23 first.
Once installation has completed, please review the Indicators of Compromise (IOC) as listed in the below post and the associated advanced hunting queries.
HAFNIUM targeting Exchange Servers with 0-day exploits - Microsoft Security
Cheers,
Rhoderick
thanks, does KB5000871 supersede KB4602269 or both required?
Hi Andy,
Yesterday's release includes the previous security fixes. No need to do both.
KB4602269 was the February 2021 security release.
Cheers,
Rhoderick