At a recent engagement a customer wanted to quickly scan through multiple servers to easily determine which services were set to log on as non-standard accounts, i.e. ones like network service, and local service were OK, but which ones were using an Active Directory logon for example? They also wanted to search specific portions of the AD, so logic was added to start searching a collection of computers from a given OU.
We took the opportunity to quickly knock up a PowerShell script to leverage the Windows 2008 R2 AD cmdlets in combination with WMI to show which services on multiple computers were using specific credentials. Please find the script attached to this blog post.
While the Get-Service cmdlet is able to query services on remote machines using the -ComputerName parameter it is not able to interrogate the Log On As information for a service. WMI is able to do this, and by using the Get-WMIObject cmdlet it was simple to query for the desired logon information.
Note that the OU path is set in the script, and unless you work for TailspinToys.com you will have to edit the OU path to reflect the correct structure.
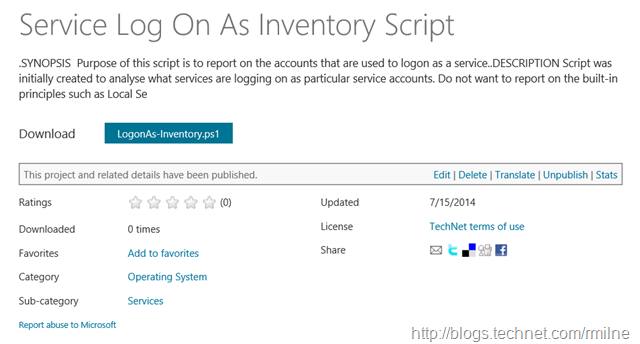
Update 15-7-2014: The script was previously stored on the blog, but since a recent blog upgrade has blocked adding/editing attached files the script has been moved to the TechNet gallery:
Update 17-6-2020: The script has been moved to GitHub.
Cheers,
Rhoderick