You have just deployed a shiny new Windows 2012 R2 member server, and joined it to the domain. After the server has restarted you try and ping it from one of the other domain machines, but ping is dropped. You check the Network Location Awareness, as you have been burnt by that before, but that is fine and it can see the AD domain.
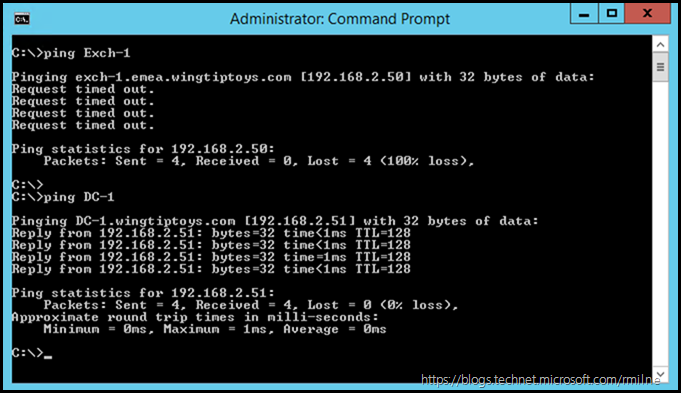
In the below example, note that the DNS request was successful. The name was resolved to an IP address, yes it is the correct one, and then the ICMP requests time out. What may also confuse matters is that other machines do respond to the ping requests. Note that the DC does respond, but the other server does not. Exchange is not yet installed onto that machine.
What typically happens at this point is that the Windows Firewall is disabled, and since ping now works the firewall is never re-enabled. This is not a good security practice at all. We aim to have defence in depth, and host based firewalls are one part of a holistic solution. Much better to figure out what is driving the behaviour, and then we can address it.
Default Windows Firewall Behaviour
Windows firewall was introduced way back with Windows XP SP2. XP SP2 was a huge overhaul, and introduced many security features. Windows Firewall is present and enabled by default in Windows today. Depending on the Windows roles and features which are installed, you will find different Windows Firewall rules enabled. This is an action which is performed when the role or feature was installed. These rules are required for the role or feature to function.
This accounts for the difference observed above. The domain controller responded, but the bare-bones OS did not. Why?
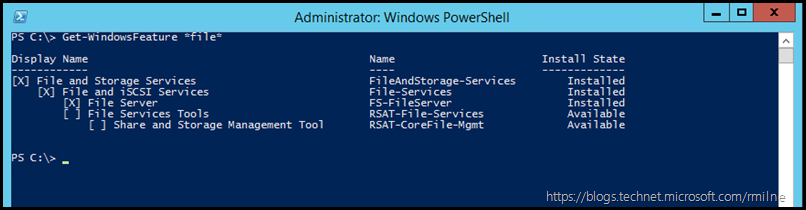
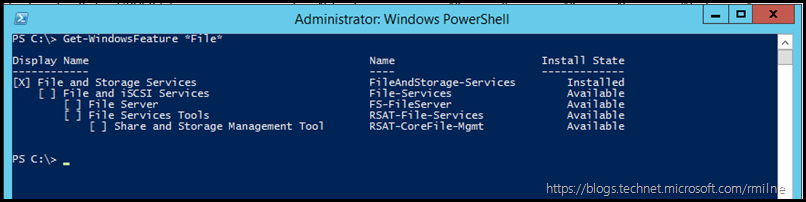
The installation of the AD DS role also adds the File Server role, and File Server role enables its Windows Firewall rules to allow ping. This is illustrated below.
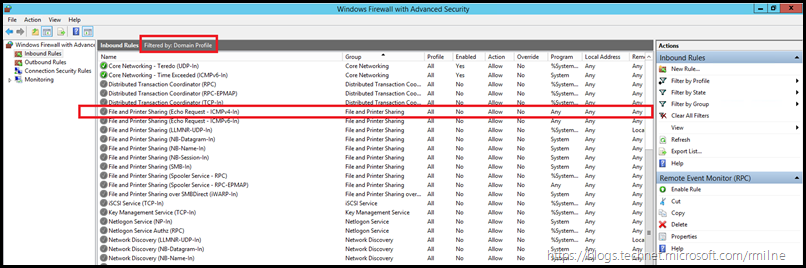
Windows 2012 R2 Domain Controller
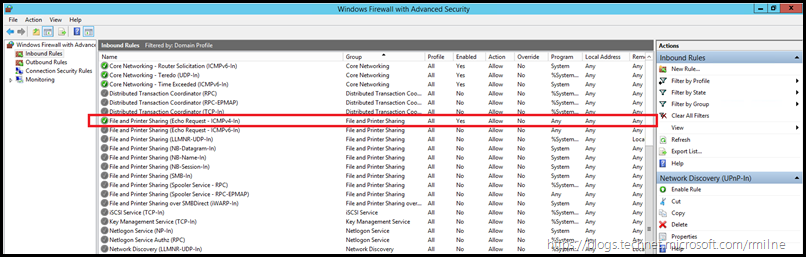
Windows 2012 R2 Member Server. Note that the File Server role is not installed.
Enabling IMCP v4 Using PowerShell
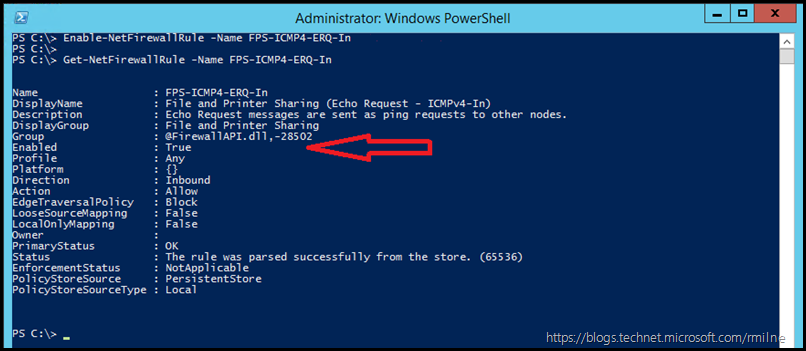
To enable the File and Printer Sharing (Echo Request - ICMPv4-In) rule in PowerShell we can use the below commands. Firstly we enable the rule, it applies to all profiles, and then we check the status:
Enable-NetFirewallRule -Name FPS-ICMP4-ERQ-In
Get-NetFirewallRule -Name FPS-ICMP4-ERQ-In
Note that there is a separate rule for IPv6, this is the rule called File and Printer Sharing (Echo Request - ICMPv6-In). You can also use the reference it using FPS-ICMP6-ERQ-In, see the note at the end of this post on the difference between these long and short names.
Enabling IMCP v4 Using MMC
There are a couple of ways to launch the graphical configuration tool. You will find Windows Firewall with Advanced Security listed under Administrative Tools. Alternatively you can run WF.msc and it will launch. The console is shown below. Note that the rules are filtered so that only the domain profile ones are shown. The File and Printer Sharing (Echo Request - ICMPv4-In rule is highlighted in the large red box.
Right click to enable the rule, and the status will change from grey to green.
Note that there is a separate rule for IPv6, this is the rule called File and Printer Sharing (Echo Request - ICMPv6-In).
Windows Firewall Intricacy
In the above examples, you will have noticed that the below syntax was used to work with the firewall rule:
Get-NetFirewallRule -Name FPS-ICMP4-ERQ-In
The Name attribute was used rather than DisplayName. This was to make the output more readable. The example below has the full display name of the rule, and since it has spaces must be enclosed within quotes. It is a bit more cumbersome to type and read.
Get-NetFirewallRule | where {$_.Displayname -like "File and Printer Sharing (Echo Request - ICMPv4-In)"}
Bonus
Now that you can adjust the individual Windows Firewall rule for ICMP, the next one you will typically want to review is the rule to allow SMB. This will allow you to connect to shared folders on the remote machine.
Hint - it is called File and Printer Sharing (SMB-In)
Cheers,
Rhoderick
Thank you for your lucid explanation of the SMB and ICMP rules.
I see so many pages where they advise to create a new rule... no thanks.
If there is an existing rule, as you demonstrated, I much prefer to use those.
I'm doing Hyper-V 2012R2 on non-SLAT processors to support WinXP VMs for clients that have business software hard coded for WinXP only.
There are many, many steps to discover for configuring the host and managing it from a Win10 desktop.
Thanks again.