The below is an interesting result after installing Exchange. The act of installing Exchange will change how TCP/IP operates on the server with respect to ephemeral connections.
This may manifest itself in a few ways.
For example:
-
Security or Network are "surprised" with different network behaviour on an Exchange server when reviewing captures
-
Network team sets a very restrictive firewall ACL which is limited to only the standard ephemeral port range, and Exchange networking is impacted
-
Profiling was performed on a regular server, and the behaviour does not match Exchange
Let's take a brief look at how Exchange is configured, and what it looks like from a tools and troubleshooting perspective.
Port Ranges
We can group ports into three main categories:
Well Known Ports 0 - 1023
Registered Ports 1024 - 49151
Ephemeral Ports 49152 - 65535
Different names can be used for each category. The well known ports are also known as system ports. Registered or User ports are used for the second category. Ephemeral are also known as dynamic or private ports.
Both system and user ports can be used to represent the port an application is listening on. IANA and Wikipedia have pages which list known applications and their respective port. The port ranges apply both to TCP and UDP.
Microsoft platforms now adhere to these recommendation. To comply with Internet Assigned Numbers Authority (IANA) recommendations, Microsoft has increased the dynamic client port range for outgoing connections in Windows Vista and Windows Server 2008. The new default start port is 49152, and the new default end port is 65535. This is a change from the configuration of earlier versions of Windows that used a default port range of 1025 through 5000.
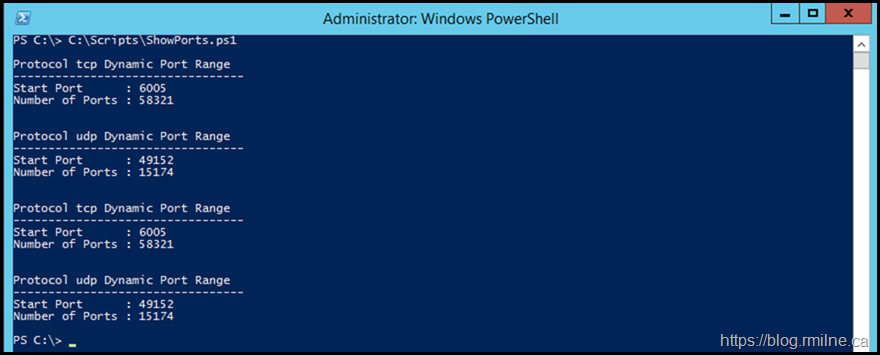
If you want to view the relevant configuration, run these commands:
netsh int ipv4 show dynamicport tcp
netsh int ipv4 show dynamicport udp
netsh int ipv6 show dynamicport tcp
netsh int ipv6 show dynamicport udp
Key Note: The default dynamic port range for TCP/IP has changed since Windows Vista and in Windows Server 2008.
Exchange and Port Ranges
However, Exchange does something a little bit different. Starting with Exchange 2007, when you install Exchange the installation routine will modify the port range. Exchange 2003 scalability was limited by the underlying x86 architecture and the associated system and memory pressures. Exchange 2007 moved to x64 and freed us of that challenge. It did raise up new scalability challenges with Outlook Anywhere though. Recall that a single user accessing just their mailbox via Outlook Anywhere (OA) would consume a minimum of 4 TCP ports.
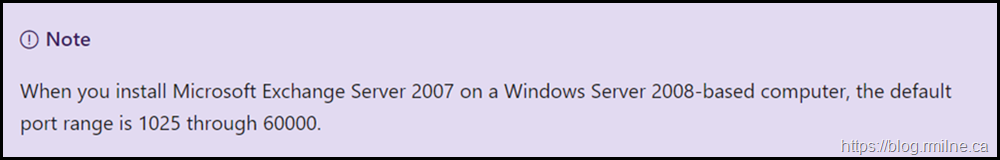
From the same article there is a note referencing this change:
Examples
The below are included as a reference and as examples to what you will see when looking at network traces or the server configuration.
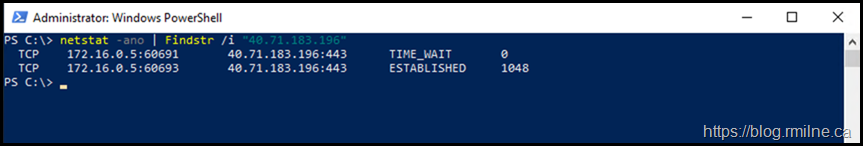
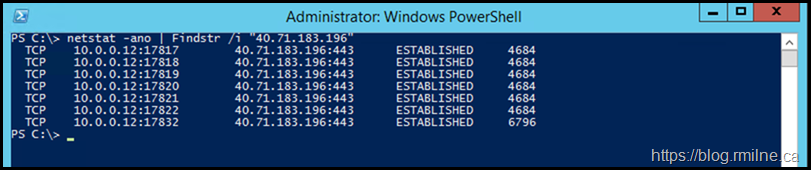
Traffic was generated by browsing to this blog, IP 40.71.183.196, and then searching the connections looking for that destination IP.
For example:
netstat.exe -ano | Findstr /i "40.71.183.196"
A current Windows 10 client is shown first, then a range of different versions of Exchange.
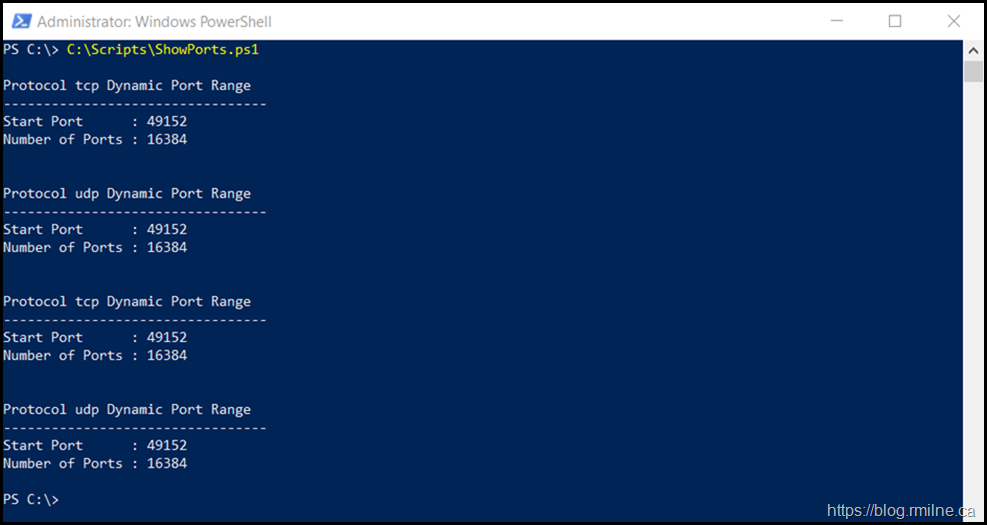
Windows 10 20 H2
This is a Windows 10 client. Adding the start port and number of port values gives a total of 65,536.
If we browse to a website (this blog) and look at the connections to the IP we can see that the ephemeral ports used are in the expected range. In the image below you can see ports TCP 60,691 and 60,693 are used.
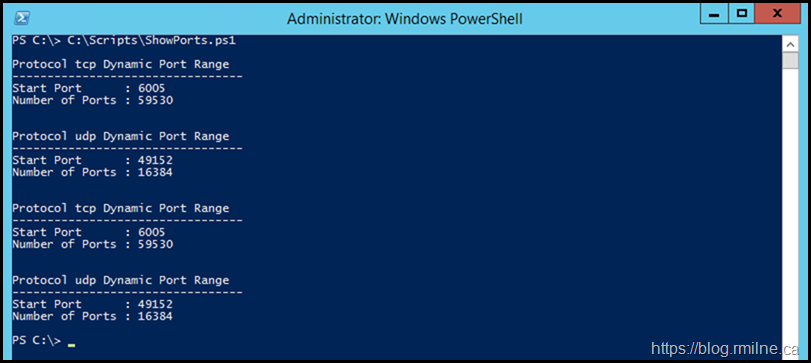
Exchange 2010 SP3 RU32
Installed on Windows Server 2012 R2. Note the difference between UDP and TCP ranges.
The sum of start and range = 655365
Note that the ephemeral port ranges used on this Exchange 2010 server are different than the Windows 10 client. The ephemeral ports are all in the 17,000 range.
That is because this is a perfectly valid range since the registry was update to use this different range.
Exchange 2013 CU23
Exchange 2013 CU23 on Windows Server 2012 R2
Exchange 2016 CU20
This is Exchange 2016 CU20 installed onto Windows Server 2016.
Bootnote
We will not discuss how TCP 60,000 and 60,0001 were proposed as a candidate for the Mail and Address Book service in Exchange 2010.
Same goes for the default DAG replication port of TCP 64,327.
Cheers,
Rhoderick