Today is patch Tuesday for February 2019 and contains a security advisory bulletin for Exchange 2010. Due to the way that Exchange 2010 is serviced, security updates are released as a new update rollup (RU). Separate updates were also released for Exchange 2013, Exchange 2016 and Exchange 2019.
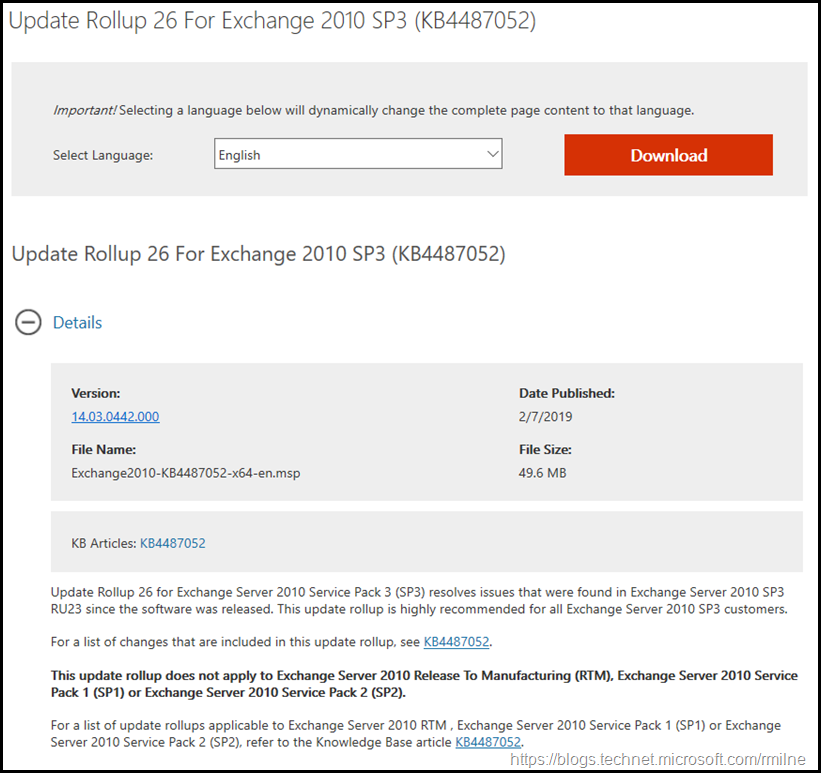
This is build 14.03.0442.000 of Exchange 2010, and KB 44687052 has the full details for the release. The update file name is Exchange2010-KB44687052-x64-en.msp.
Note that this is only for the Service Pack 3 branch of Exchange 2010. Why? Exchange 2010 SP2 exited out of support on the 8th of April 2014 and will no longer receive updates. Customer must be on Exchange 2010 SP3 to receive updates.
Also note that Exchange 2010 transitioned into its Extended product support lifecycle phase on the 13th of January 2015. Exchange 2010 will now be serviced as per the extended support policy.
Exchange 2007 is no longer supported, updates are not provided once a product has exited out of extended support.
Exchange 2010 will transition out of support on the 14th of January 2020.
Issues Resolved
This release of Exchange 2010 addresses the security issues described in Microsoft Common Vulnerabilities and Exposures CVE-2019-0686 and Microsoft Common Vulnerabilities and Exposures CVE-2019-0724 which are linked from https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/adv190007.
See also Security Advisory ADV190004.
Note that there are changes in Exchange EWS functionality with this release, so please review all of the notes contained within the release post.
Customers with only Exchange 2010 present will need to follow KB 4490059 -- Reducing permissions required to run Exchange Server by using Shared Permissions Model. Exchange 2010 setup will not make these changes.
If a newer version of Exchange is present alongside Exchange 2010, then the setup process for latest version of Exchange present can be used.
Note that Exchange 2010 SP3 RU26 now supports installing on to Windows Server 2012 R2. This change was announced in the The Microsoft Hybrid Agent Public Preview post.
Important Notes
The below are the normal notes to consider before deploying an Exchange RU. In this case, the below must also be tempered with the fact that there are security fixes.
There are a couple of items to mention:
- Test the update in your lab before installing in production. If in doubt test…
- Follow your organisation’s change management process, and
factor the approval time into your change request. - Provide appropriate notifications as per your process. This may be to IT teams, or to end users
- Place the server into SCOM maintenance mode prior to
installing, confirm the install then take the server out of maintenance mode. - Place the server into Exchange
maintenance mode prior to installing, confirm the install then
take the server out of maintenance mode.
- Ensure that you consult with all 3rd party vendors which exist as part of your messaging environment. This includes archive, mobility and management services.
- Ensure that you do not forget to install updates on management servers, jump servers/workstations and application servers where the management tools were installed for an application. FIM and 3rd party user provisioning solutions are examples of the latter.
- If the Exchange server does not have Internet connectivity then this introduces significant delay in building the Native images for the .Net assemblies as the server is unable to get to http://crl.microsoft.com. To resolve this issue, follow these steps:
- On the Tools menu in Windows Internet Explorer, click Internet Options, and then click the Advanced tab.
- In the Security section, click to clear the Check for publisher’s certificate revocation check box, and then click OK.
We recommend that you clear this security option in Internet Explorer only if the computer is in a tightly controlled environment. When setup is complete, click to select the Check for publisher’s certificate revocation check box again.
- I personally like to restart prior to installing updates. This helps identifies if an issue was due to the RU or happened in this prior restart, and also completes any pending file rename operations. 3rd party AV products are often guilty of this.
- Restart the server after installing the CU.
- Ensure that all the relevant services are running.
- Ensure that event logs are clean, with no errors.
- Install the update from an elevated command prompt.
- Ensure that the Windows PowerShell Script Execution Policy is set to “Unrestricted” on the server being upgraded or installed. See KB981474.
- Update Internet facing CAS servers first.
- Backup any OWA customisations as they will be removed.
- Uninstall any Interim Updates (IUs) before installing the RU. You will have received these private files directly from Microsoft.
- Disable file system antivirus prior to installing the RU.
- Restart server after RU has been installed and then re-enable file system antivirus
- Test (yes, technically this is in here for a second time but it is very important!)
Cheers,
Rhoderick