Below are a series of links to the main Microsoft Defender for Office 365 blog. Shortcuts added here as this is one of my shared bookmarks.
Note that some links have KQL queries and IOCs related to that specific attack.
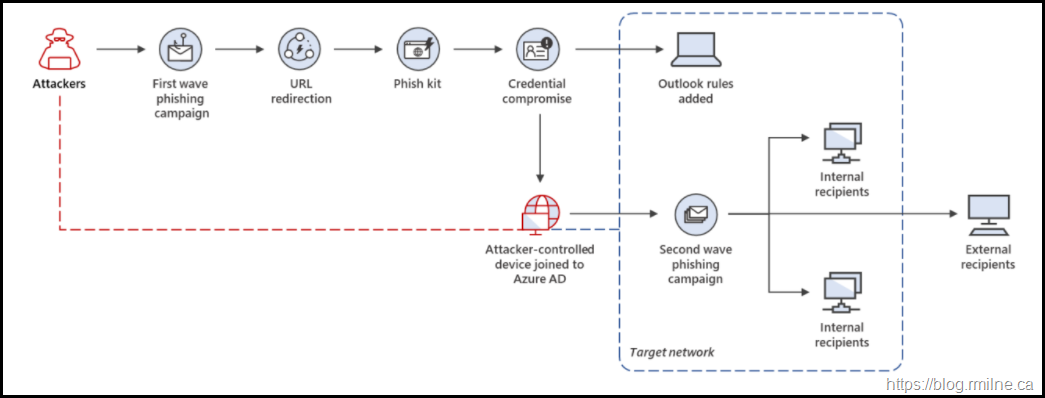
From cookie theft to BEC: Attackers use AiTM phishing sites as entry point to further financial fraud
12-July-2022
Evolved phishing: Device registration trick adds to phishers’ toolbox for victims without MFA
26-January-2022
Note that compromised end user connected to EXO as part of this attack.
Trend-spotting email techniques: How modern phishing emails hide in plain sight
18-August-2021
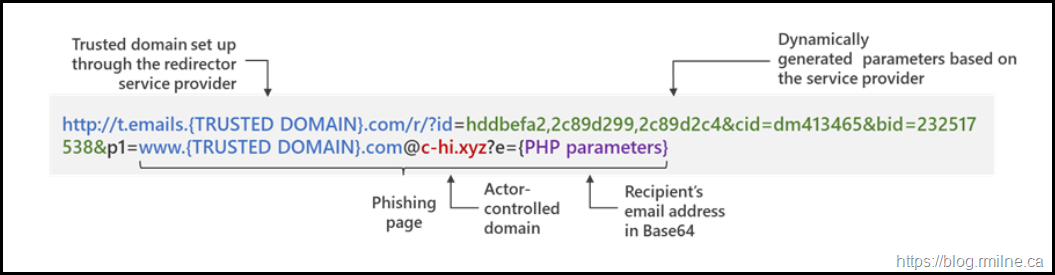
Widespread credential phishing campaign abuses open redirector links
26-August-2021
Protect against phishing with Attack Simulation Training in Microsoft Defender for Office 365
16-November 2021
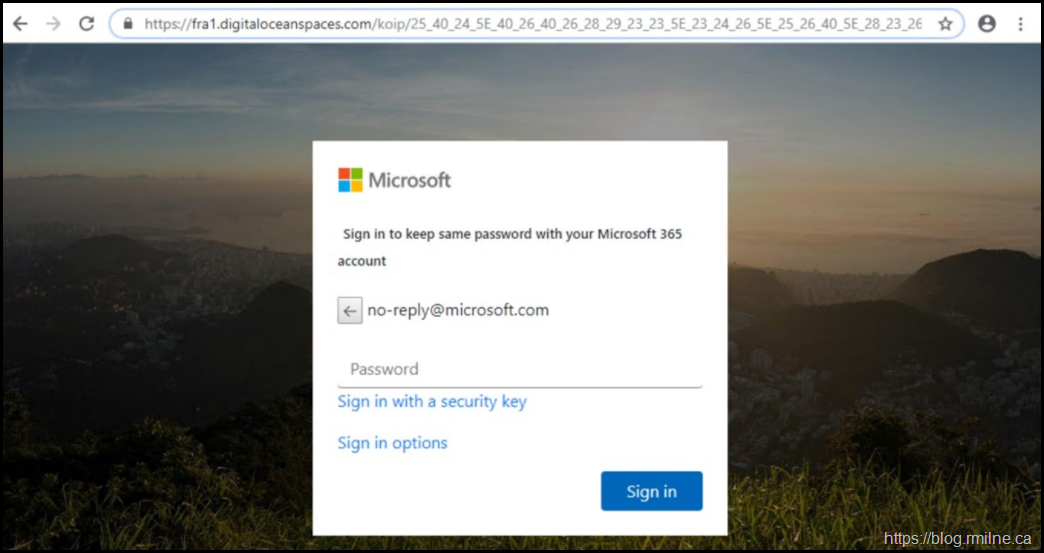
Franken-phish: TodayZoo built from other phishing kits
21-October 2021
Catching the big fish: Analyzing a large-scale phishing-as-a-service operation
21-September-2021
Get free DMARC visibility with Valimail Authenticate and Microsoft Office 365
1-September-2021
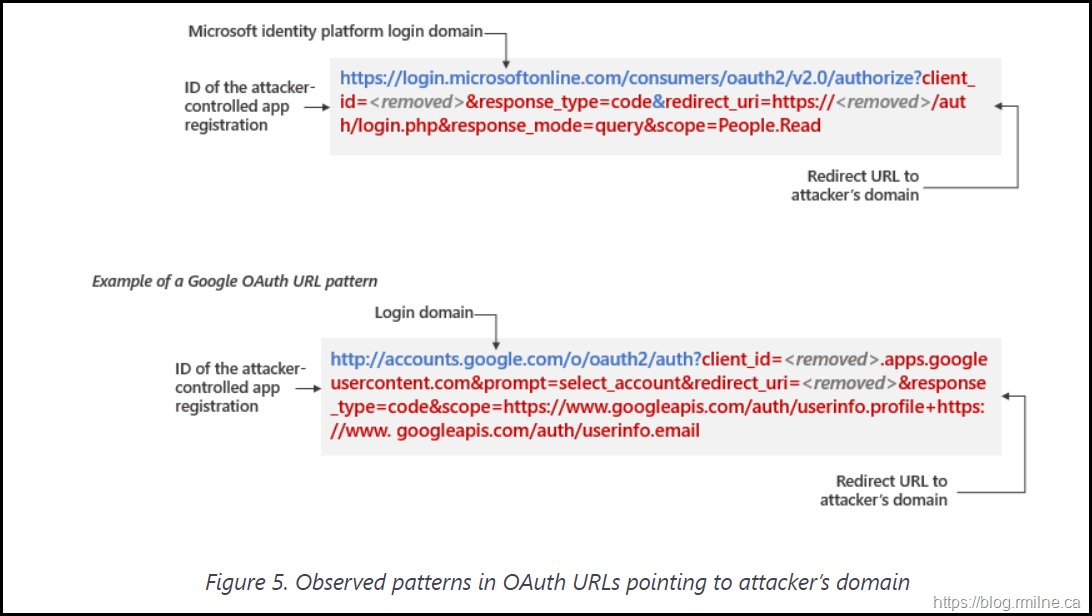
Microsoft delivers comprehensive solution to battle rise in consent phishing emails
14-July-2021
See also the documentation to protect against conscent phishing.
Behind the scenes of business email compromise: Using cross-domain threat data to disrupt a large BEC campaign
14-June-2021